9 Tips to Keep your Networked Computer Safer
Earlier this week the New York Times reported a story on a large scale electronic payment scheme aimed at Brazil. Hundreds of thousands of computers are potentially affected, and it is estimated that the equivalent of billions of dollars have been pilfered. However, you don’t have to be sending “Boletos” to be an appealing target. Any login or credential information you use on your computer is appealing and has potential value to cybercriminals.
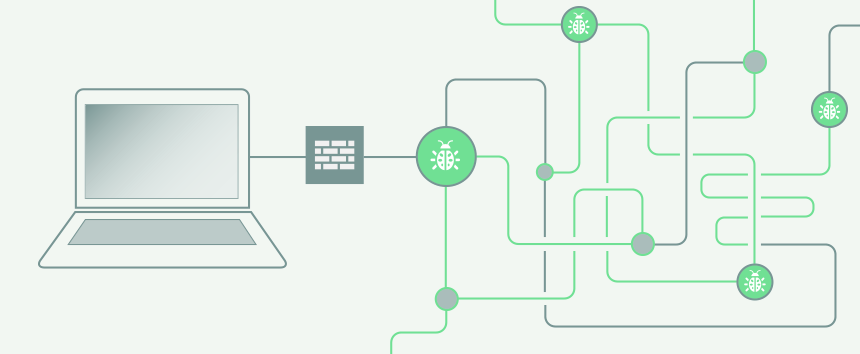
With ever-increasing use of personal devices and laptops on networks everywhere, it’s more important than ever to be mindful of information security. For example, just visiting a malicious web site can compromise a vulnerable computer, and enroll it in a botnet. The computer may appear to be functioning normally, but it is serving more than one master. Botnets such as “Kelihos” can install additional malware, which (among other things) can monitor outgoing traffic on well-known email and FTP ports, watching for passwords and other interesting traffic. It can also listen to other computers on the same network segment (depending on the network topology), capturing credentials if they are sent in the clear. These captured credentials are aggregated and sold by whoever is controlling the botnet.
Even if your laptop or device is not compromised, you can’t be sure about all of the other devices owned by people in your network. You could be vulnerable to malware installed on their computer.
Here are 9 tips to help practice good IT hygiene:
- Passwords should be long and strong, and different for each service you use.
- Keep your software defenses (firewalls, browsers, etc.) up to date.
- Use well-regarded personal firewalls on your computing devices.
- Use anti-malware and anti-virus tools. Different tools detect and nullify different threats.
- Perform periodic scans of your computer even if it’s only on “trusted” networks.
- Be very careful about opening links or documents sent to you via email. Don’t know the sender? Don’t open the document.
- Make sure that you use encrypted protocols, like HTTPS for web traffic, encrypted FTP (FTP with TLS, or SFTP), and encrypted SMTP. If a nosy, compromised neighbor on your network segment is listening, they won’t be able to capture your credentials in the clear.
- Avoid risky online behaviors. If the information on your laptop is critical to your livelihood, make sure you have multiple, time-separated backups. Don’t mix business and leisure on your computing devices.
- Use multi-factor authentication for access to important or valuable resources, so if your computing device is compromised, the attacker will have greater difficulty using your credentials
This list is by no means exhaustive. With ever more advanced security for personal computers you can always “go deeper” to protect your computer’s vulnerabilities. Don’t get complacent about security. Even “safe” networks can be vulnerable, so don’t think your device is safe just because you’re not using a public network.